Security Chronicles: 10 Security Tips For The Everyday User
by 19 April, 2013 6:35 am0

#1 The Golden Rule
The Golden Rule is the first line of security against the nastier bits of the online world. The rule is simple: common sense. So don’t accept emails from Nigerian exiles, international bankers, free pharmacies, random women who want to share their pictures with you, etc. If an email, IM or link features ridiculous or suspicious content from an unknown contact, then just mark it as spam or delete it immediately.
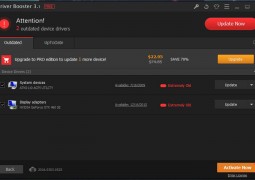
#2 Free Anti-Virus & Free Firewall
Antivirus protection is essential for anyone using a computer (Macs included!). What is not essential is one of those high-priced security software systems that drain your wallet and processing power. Assuming you stick to the golden rule, a reasonable anti-virus system is good enough. If you are running a genuine version of Windows, you are entitled to a free version of Microsoft Security Essentials (MSE) that is both lightweight and effective. You could also use a free version of AVG, Avira, Avast or Comodo.
The same principle applies to the firewall mechanism. Microsoft’s integrated firewall is good enough but you could also use a free firewall version from Comodo, Zone Alarm, etc. If you are a fan of layered security, you could use one security software for Antivirus and another for your firewall.
#3 Passwords
Numerous studies show that passwords used by a lot of people are far too predictable. Even if you are settling for a simplistic password, make sure it utilizes a combination of numbers, symbols and capital letters. For example, if I were to use my name as the password it could be entered as “N@vam N1le$”. Have fun with your password, use a word or phrase you are familiar with because you don’t want to be in a position where you must write the password and stick it to your desk.
Try to avoid using the same password for different email addresses or special accounts. If you must, then add additional letters, numbers or symbols to differentiate the passwords. For example, “N@vam N1le$989” , “N@vam N1le$998”, “N@vam N1le$899”.
Also, if you are using an unknown or unsecured computer that might feature a keylogger, ensure that all passwords are copy-pasted into the password box.
#4 Secure Unused Email Addresses(s)
We have all probably migrated across different email clients at some time or the other. If you are like me, the primary email address is also linked to the secondary email address, which creates security vulnerability. Therefore, it is vital to secure secondary email addresses. If you are not using them, at-least make sure that you have access to the accounts at all time. Or else, you could remove the account altogether and use a different recovery system for your primary email address (mobile code, secret question, etc.)
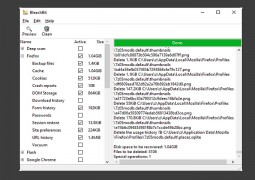
#5 Update Your Software
Software that is up-to date is probably the most effective way of avoiding unnecessary security lapses. If you are on Windows or Mac, set your updates to download automatically or at-least alert you when they are ready. Critical updates for Windows and Mac are essential. It is also important to ensure regular updates for browsers, antivirus/firewall updates, general software, etc. For software that is critical to security, updates should be set to automatic at best or semi-automatic (alerts when updates are available or ready for installation) at worst.
#6 Monitor Linked Accounts
Some apps and websites allow users to login with a Google Account or Facebook. It is important to keep track of those apps and remove them if necessary. These apps usually collect a lot of data and they could render your personal data vulnerable. So login to your Google or Facebook accounts periodically and review the apps linked to your account. If you were no longer using the apps, then it would be better to remove them all together.
#7 Get Chrome
Chrome is arguably the most secure browser out there. In terms of security, the browser alone is an important element, especially because so many of us spend a bulk of our time online. Google’s browser users a “sand-boxing” mechanism to isolate one tab from the other and the browser from your OS. This prevents malicious code spreading and infecting the whole system. Google is so confident of their security that it invite the brightest hackers in the world to compete at the Pwnium Security in an effort to hack into Chrome but so far no one has taken the top prize. Furthermore, some of the recent privacy and security features, along with the advanced synchronization option, allows users to strike a good balance between security and performance.
#8 Don’t Buy Pirated Copies of Anything
Avoid pirated versions of software, which could pose a direct risk to your digital security. This is especially true for pirated versions of Windows. In some cases, the virus files are part of the OS’s critical files. In this case, Trojans and other nasty bits can identify themselves as part of the OS and either avoid or evade the anti-virus system until it is too late. One solution is to use open source. Chrome, Ubuntu, Linux and others are quickly emerging as viable (not quite there yet) options. Moreover, online apps are quickly giving more established apps a run for their money (e.g. Google Drive, Open Office, etc.)
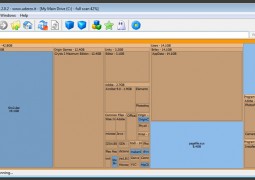
#9 Backup Your Data
No security plan is fool-proof so and it is possible to lose all your data (e.g. laptop stolen, virus infection, remote wipe, etc.) so make contingency plans. One of the most important things is a backup of your critical data. There are plenty of ways to get around this. The obvious method is to go around with a high-capacity external hard-drive and periodically back-up the data on your Mac or PC. Get into a good habit of doing this at-least once a week.
Another method is to upload your critical data onto the cloud. Popular apps such as Google Drive,SkyDrive, DropBox, iCloud(for Macs) and others are viable options. When it comes to costs, it really depends on the capacity of the storage. Right now, Skydrive is better for lower-capacity options while Google Drive is more cost-effective for high-capacity storage options. While the others fall somewhere in between. Backing up your data on the cloud is more convenient (you could lose your portable hard drive but it is difficult to imagine multiple servers from Google or Microsoft failing simultaneously – the odds are too low in that case).
#10 Security Compartmentalisation
 I had a colleague of mine who lost his MacBook Air and he made the mistake of leaving it logged-in. If he had sensitive data, all the thief would have to do is to open the lid to gain full access. What I mean by security compartmentalisation is a security policy that delays or prevents a thief or hacker from gaining full access to your PC. The first step is your password. Use a boot-up password and also use a password for your Windows/Mac User account. Make sure the password is required when the PC is woken-up.
I had a colleague of mine who lost his MacBook Air and he made the mistake of leaving it logged-in. If he had sensitive data, all the thief would have to do is to open the lid to gain full access. What I mean by security compartmentalisation is a security policy that delays or prevents a thief or hacker from gaining full access to your PC. The first step is your password. Use a boot-up password and also use a password for your Windows/Mac User account. Make sure the password is required when the PC is woken-up.
If you are using a Chrome browser (or anything else that allows multiple sign-in), use different user accounts to separate your data (e.g., Navam-Personal & Navam-Work). For each account, use different security policies if necessary. Therefore, for your personal account you could save passwords, install a variety of apps, sync all your data, etc. For your work account, don’t save passwords or keep material open at any times. This limits the amount of exposure to a security breach. If you are using cloud-storage, then all you need to do is change your password and access to your online files is immediately blocked.
What Do You Think About On-line Security
Are there any PC security tips you think are essential for everyday use? Let us know!